Despite barely one month into the second quarter of the year 2022, we are seeing a lot of crypto-related news making big headlines.
Crypto space & its communities
Undeniably, crypto & its communities have brought about huge changes to how things work. From normalizing 100% remote working & not having a physical space as the office to advocating the power of community, the crypto community is serious about breaking the norms and introducing new ways to how things work.
Given that bitcoin (the first cryptocurrency that spearheaded the emergence of crypto space) was first introduced & created during the 2008 financial crisis year and seeing how the pandemic years (the year 2020 onwards) have been the growth accelerator for crypto space, it is of no wonder that the crypto community seek for unorthodox ways towards how things were done.
Although most of the crypto communities gather around the space of primarily Twitter, Telegram, and Discord, the power of crypto communities was visibly seen during a few circumstances.
How Crypto Communities Contributed to Ukraine
One unfortunate event that happen this year was the Ukraine-Russia war. It was, during this circumstance that we have seen the power of the crypto community in action.
With the plead of the Ukraine government in gaining more monetary support in the form of crypto assets, they have provided the crypto wallet addresses (long numerical & alphabet as shown in the tweet below).

According to Elliptic, Come Back Alive NGO & Ukrainian Government were able to raise $63.8 million in cryptocurrency donations as of 11 March 2022.
Malaysia Flash Flood Incident that Proves There Can Be a Flash Fund too
Locally, we have seen how the crypto communities come into play with their contribution to the Malaysia flash flood.


With an initial goal of 3 BNB (approximately $1,574 at that time), the community managed to raise a total of 37.34 BNB (approximately $19,508 at that time) in just two days. The fund has been distributed to various organizations and shelters.
UN World Food Programme (WFP), An Early Adopter
UN World Food Programme (WFP) has utilized blockchain technology as early as May 2017 in Jordan for the refugee, which helps to lower transactional costs by 98%. This ensures most of the funds can be given directly to the refugee.
From the above few case scenarios, we have seen how crypto & its communities play a huge role, especially in times of need.
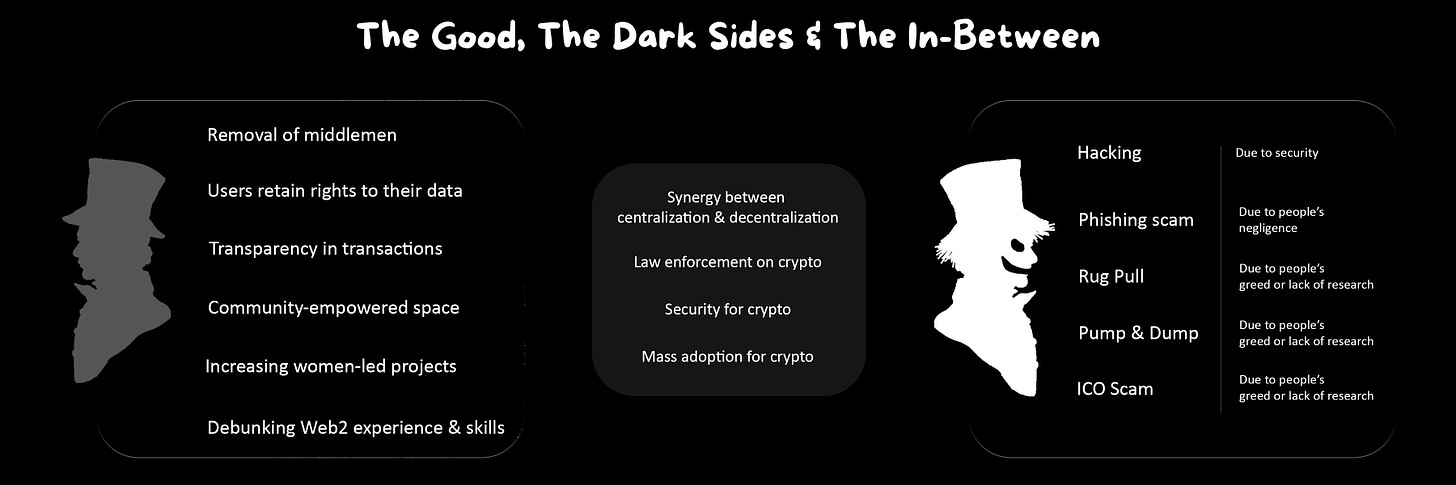
The Good Sides of Blockchain & Crypto
1. Blockchain removes the need for a middle person
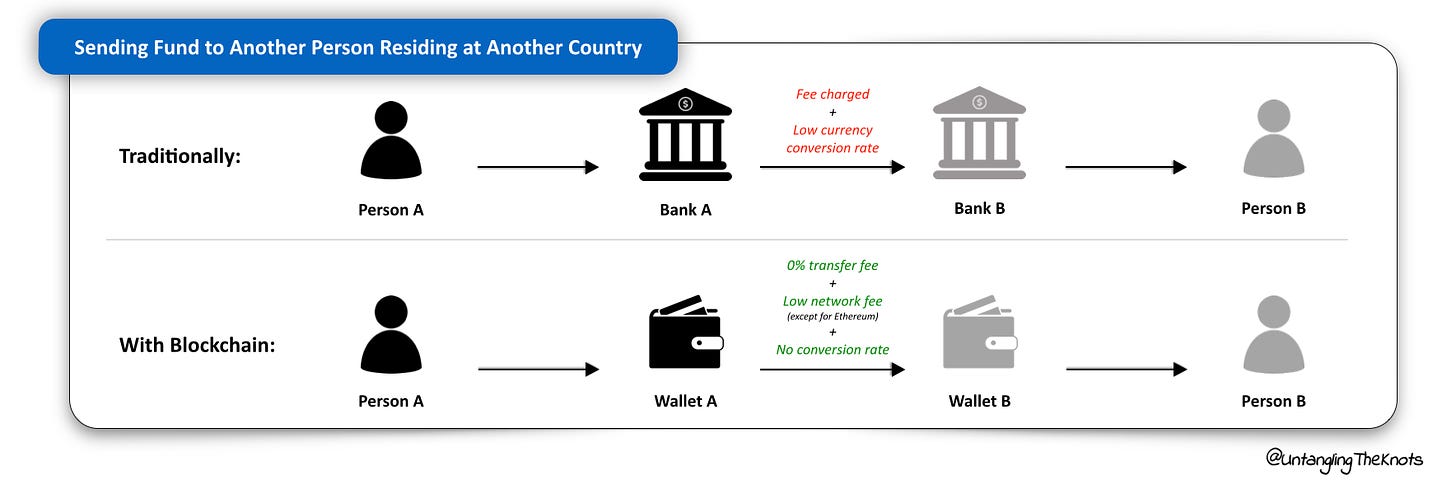
Below are two case scenarios, using visuals to show how blockchain eliminates the need for a middle person in the finance or transactional scenario.
Scenario 1 shows that the wallet, which is decentralized is used to eliminate banks & all the hefty costs charged by the banks. Instead, the user would only need to pay a low network fee (except for the Ethereum network) in order for the recipient to receive the fund in the same cryptocurrency.
In this case scenario, the company would be charged with a certain percentage from the transaction (for example FPX on the website portal).
In adopting blockchain, the company would only need to pay for the exchange rate for the cryptocurrency to be changed to fiat currency (USD, MYR), which is much lower in comparison to the charges by the bank.
2. Blockchain enables individuals to regain their rights & full access to their contents, data, assets
One of the biggest assets of the 21st century is data. We often heard the saying that goes “Data is the new gold”. And yet, we still give our own data to tech giants like Google or Facebook for free every single day, and in return, for them to be used on us.
Web 3 changes that.
With blockchain, a browser that does not keep your browsing data, a video streaming platform that does not sell you ads and use algorithms, and a financial institution that does not hold your credit data against you are how the crypto space dismantles the need for a middle person to control your data and rights.
3. Blockchain creates transparency in transactions
We have heard multiple times how blockchain is the open ledger and all the transactions that happen on the blockchain are accessible by anyone. But what does it really look like?
Let’s say that we are interested to see who holds the most expensive Bored Ape Yacht Club #2087.
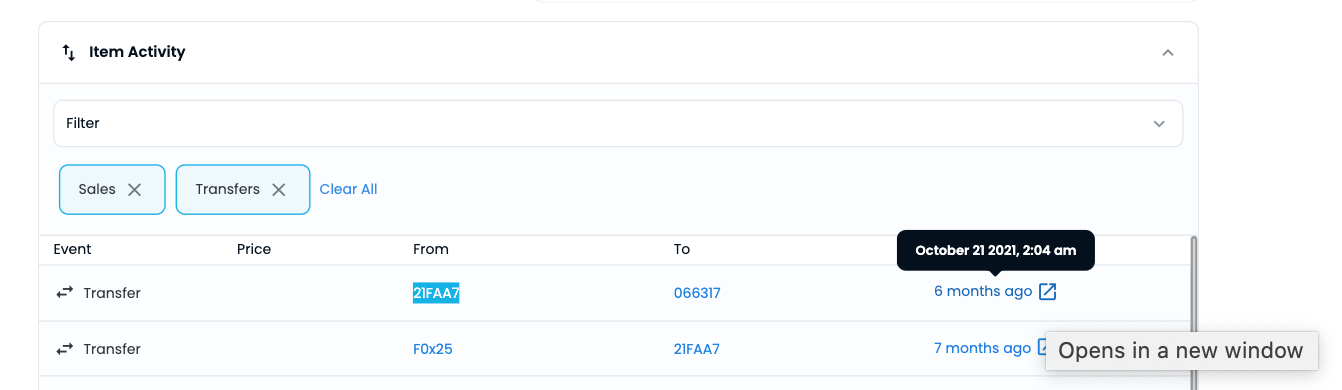
We can go to Open Sea, one of the largest NFT marketplaces, and search for BAYC #2087. Under “Item Activity”, in the latest transaction, we can see this NFT has been transferred from 21FAA7 to 066317.
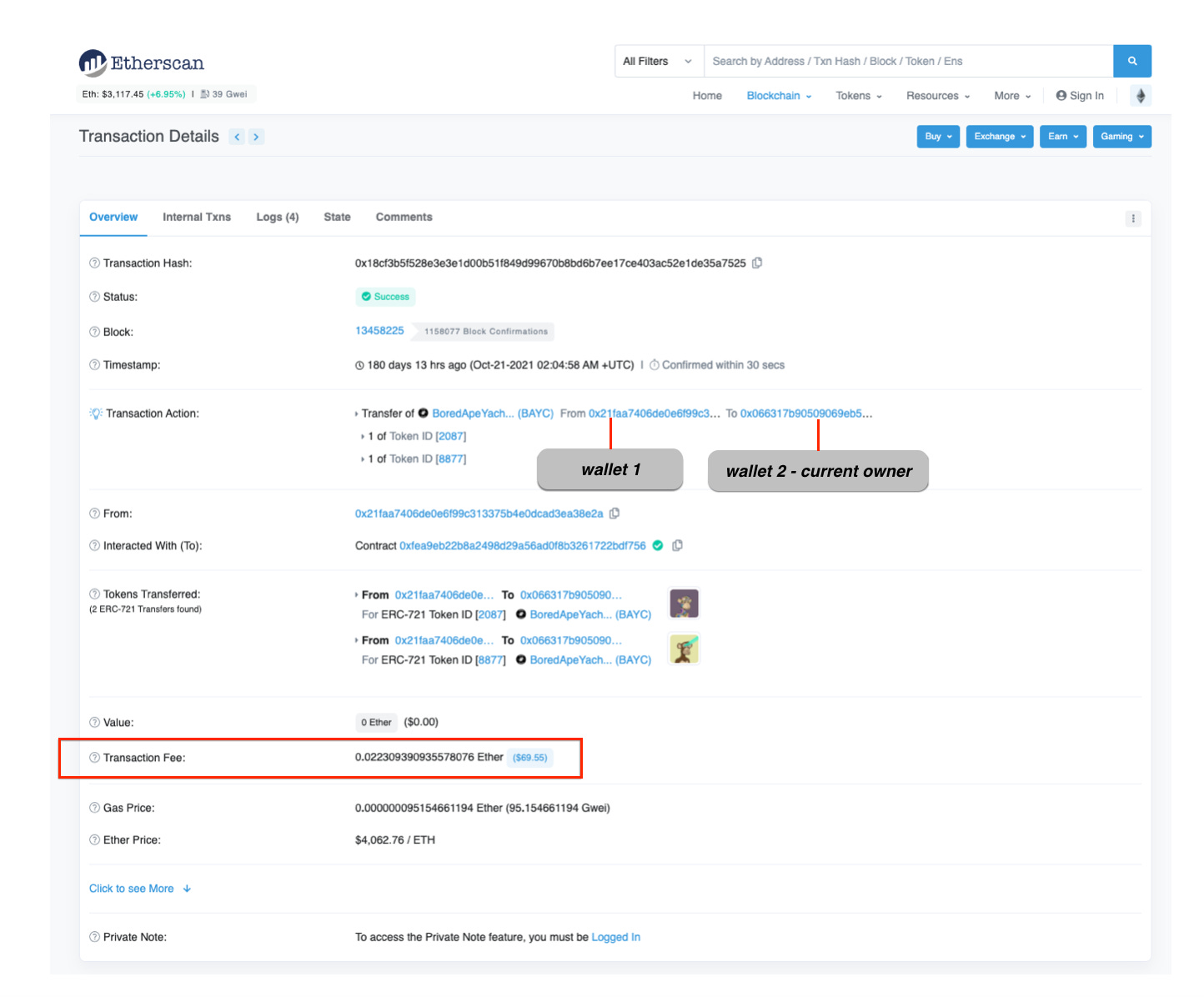
By clicking the “Opens in a new window” prompt, you will be led to Etherscan.io, a platform that keeps track of all Ethereum transactions.
On the Etherscan page, we could see all information related to that transaction, including the fees & amount the NFT paid for. In this case, it is a transfer of NFT, not a purchase, from one wallet (0x21faa7406de0e6f99c369eb5…) to another wallet (0x066317b905090…) with a total transfer cost of 0.0223 Ether ($69.55) at the time when Ether was priced at $4,062.76 per Eth.
Let’s say that I am curious what other NFTs this wallet owner holds.
What I can do is that I click on the wallet address (0x21faa7406de0e6f99c369eb5…) that is highlighted in blue & this will lead me to the Etherscan page with all the details in regards to the wallet.
The above screenshot shows the details of the wallet, where the owner has about 834 ETH tokens in his wallet which is equivalent to $2 million (excluding his total NFT valuation). The NFT collection this wallet owner has is huge, encompassing other BAYC, LV, Hermes, Mindblowon etc.
From the above showcase, it is obvious how transparent blockchain can be especially on transactions. Perhaps some might find it eerie that everyone can look into their wallet with all the details but others might find it as a way to flaunt their collection or even embrace the beauty of transparency but not at the expense of security.
4. Crypto is community empowered space
Instead of a fully top-down approach, crypto has shaped the way companies or projects do things. By taking into consideration what the community wants & providing the power to voice their opinion, these crypto companies & projects removed the barrier layer & able to get direct & real-time feedback from their communities, which essentially are their customers.
5. Crypto women-founded and empowered projects
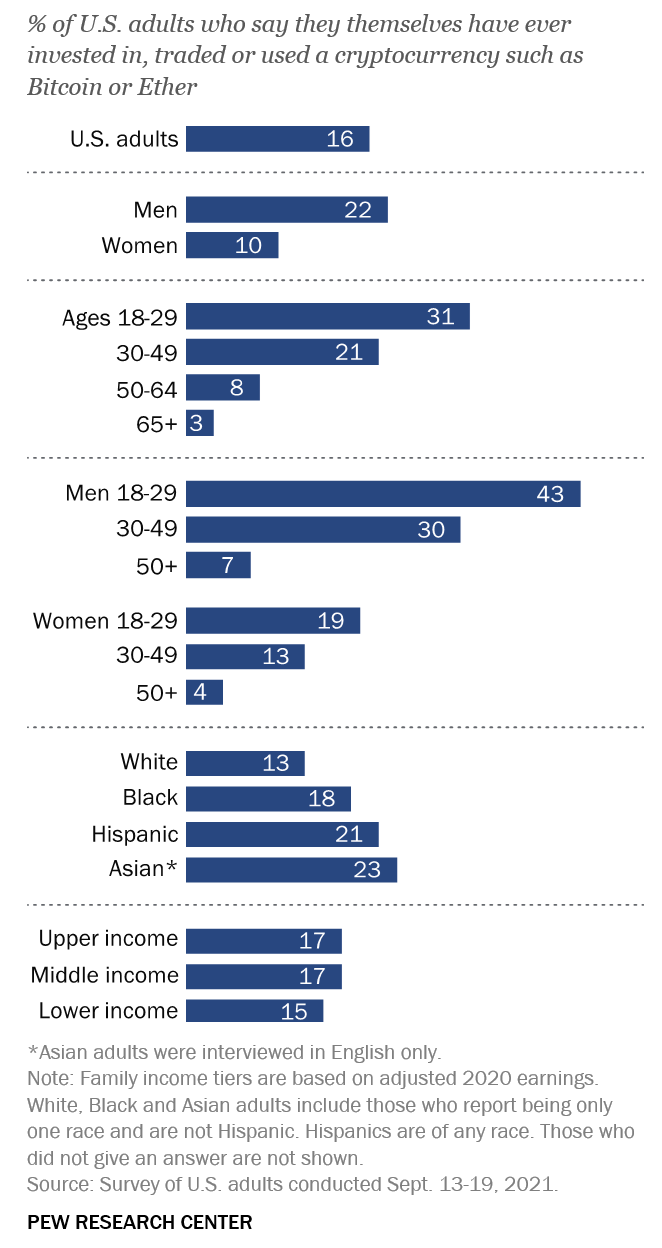
Interestingly, the increasing women-founded and empowered projects created a realization that perhaps the crypto space is too crowded with men. The imbalance disparity between the two genders within the crypto space (either as investors or partake in the crypto projects) deters most women from participating and contributing.
Creating a safe space for women in the crypto space to explore, contribute and lead is important as women make up less than half of the men in the crypto space.
Women-centric NFTs are one of the waves making strides in promoting equality and increasing representation in the NFT world and crypto.
6. Crypto space debunking Web2 skill set, age, experience & limitation of residency
The fast pace crypto environment has create a gap between the existing skill set vs skill set that is sought after. With new way of working & new system, the Web 2 skill set becomes irrelevant. While it is safe to say that the crypto space debunk the limitation that beholds onto experience, age or even place of residency, the ask from individuals would be higher as each individuals should be able to perform with agility, curiousity, accountability alongside with the elements of risk-taker due to the nature of this industry. With all the good things out there especially those related to money, it is inevitable that we will see some form of exploitation. Now that we have visited the brighter part of crypto world, it is time to delve into the darkers side.
Darker Side of The Crypto Space
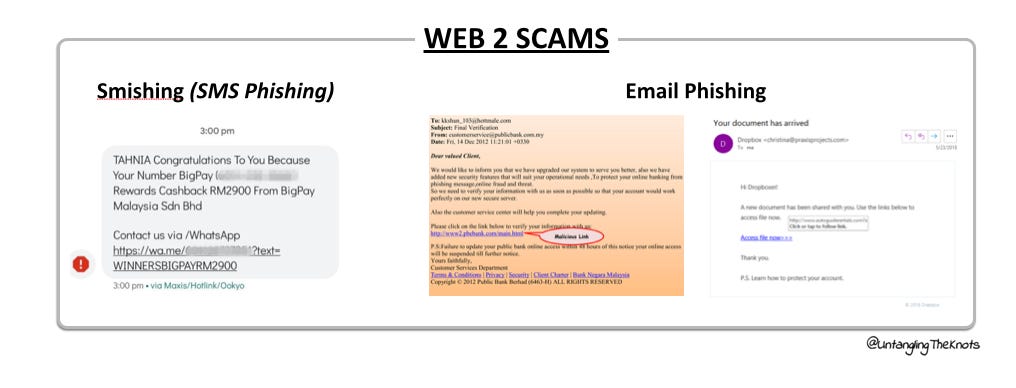
Many have perceived that the crypto space is constantly plagued with hacking activities and scammers are constantly lurking around the corners to make their next strike. It does not help that the news often painted a one-sided picture most of the time.
It is undeniable that the issue of exploitation is causing a huge concern, especially for those who may be interested in dabbling in the crypto space but get held back.
While a few are indeed due to security issues, most of them are due to people’s greed or negligence. By putting some of the past or recent events into their respective category, perhaps it is easier to paint the picture of what is happening on the darker side of the crypto space.
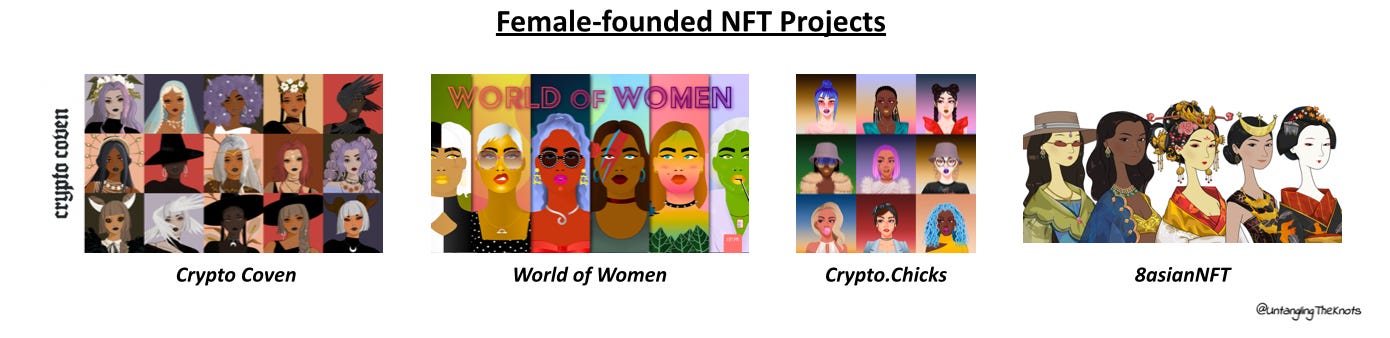
1. Hacking
Hacking is the act of breaching or compromising the security of the system for personal gain.
While most people think that crypto space is often swarmed with hacking activities, day-in-day-out, in reality, it is less frequent than perceived.
Axie Infinity (Ronin Network), the play-to-earn crypto gaming that gain popularity in SEA especially in the Philippines in 2020, fell victim to hackers, which were believed to be a group of North Korea-tied hackers. The FBI confirmed that the Lazarus Group and APT38, cyber actors associated with North Korea, are responsible for the theft.
Poly Network, a decentralized finance platform, was hit with a major attack back in 2021, but it turns out to be the work of white hackers (hackers with no ill intention) that tries to reveal vulnerabilities and secure Poly Network. The hackers then returned all the assets to Poly Network as promised while Poly Network learned the ways to secure its platform.
2. Phishing Scam
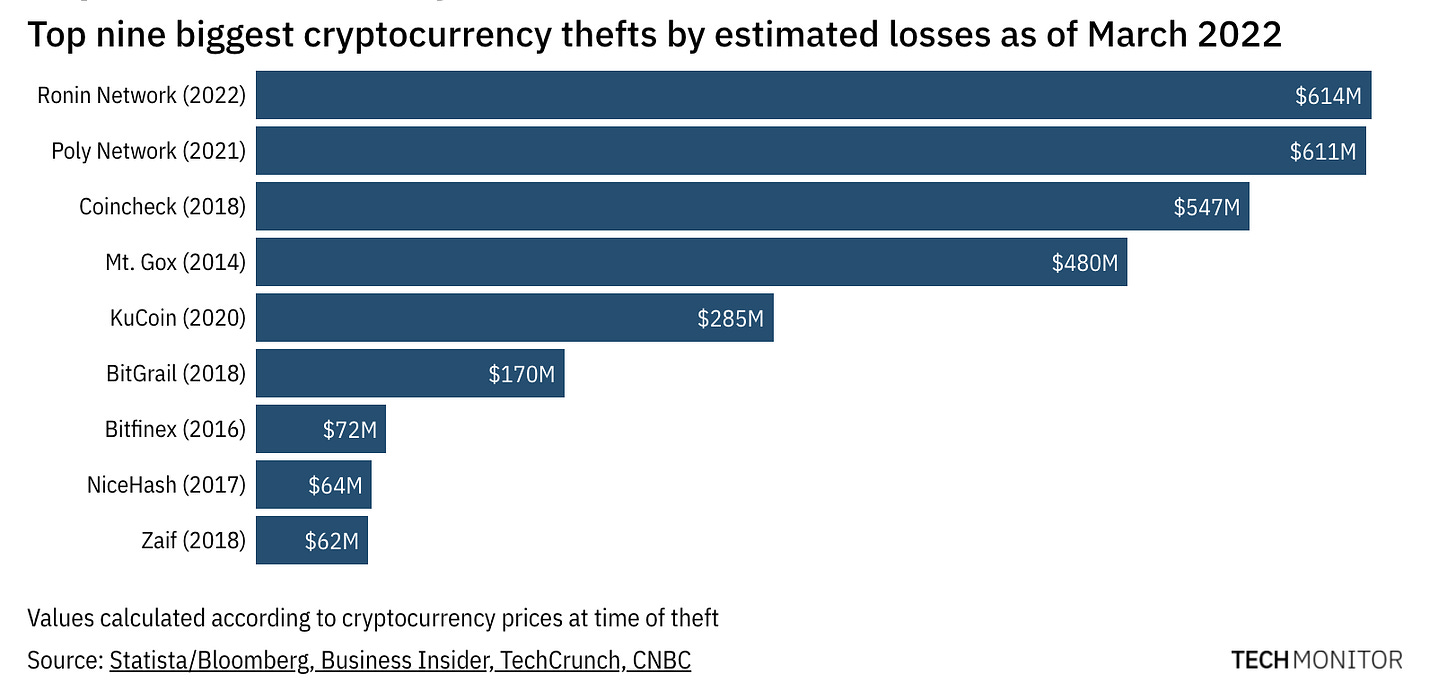
The phishing scam is a type of scam that tricks or “fish” the owners into providing details of personal information that allows these scammers to get into your bank account or garner company data.
Web 2.0 Scam - Smishing & Email Phishing Scam
There are more than 10 types of different phishing scams but the Smishing & Email Phishing scams are the most commonly known & used scams where the malicious link is attached to an SMS or Email with contents that try to lure victims to click on it & submit all the personal details.
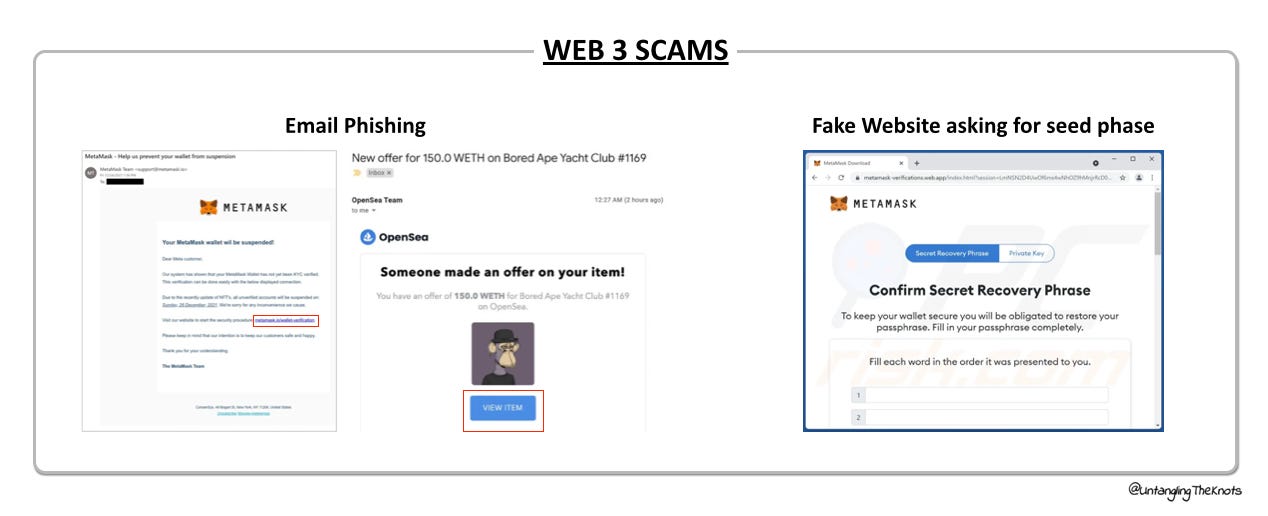
Web 3.0 Scam - Email Phishing or Website Phishing
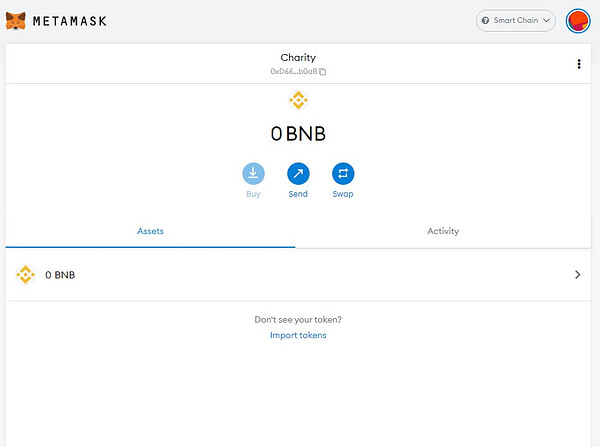
As for phishing scams for crypto, the target is on the crypto wallet as most of the crypto assets are stored there. The concept is similar to a bank account where it is quite secured on its own unless we provide certain information like our login details or bank card pin number to others.
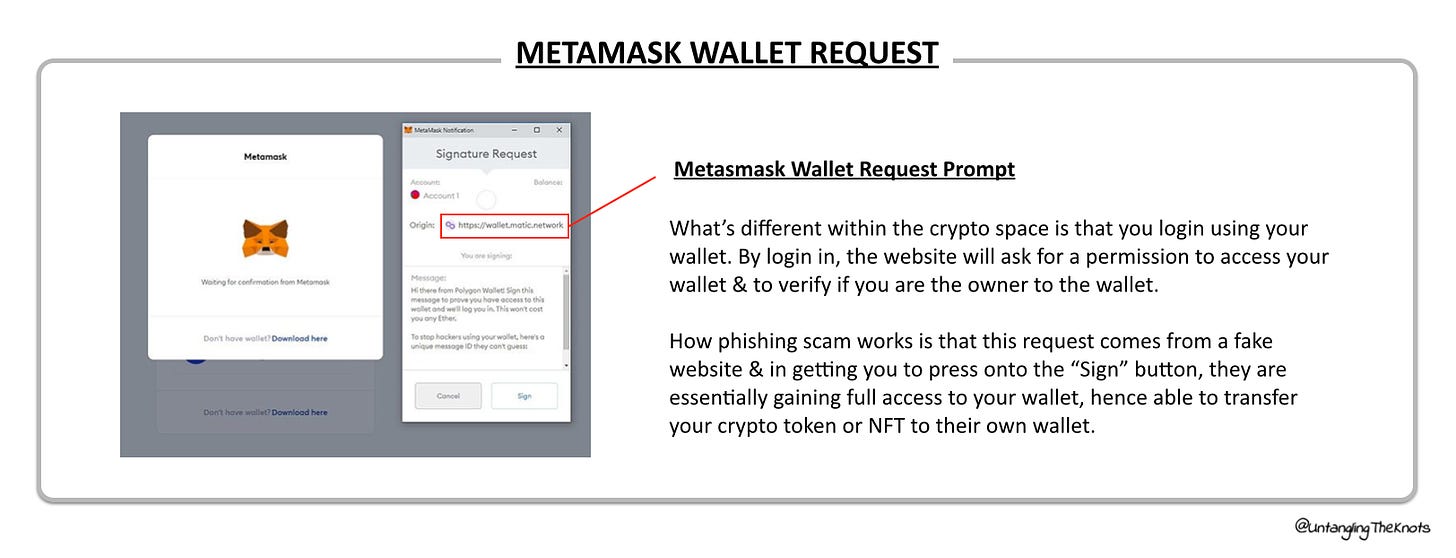
For a wallet like Metamask, you would need to have a password and seed phase in order to gain access to the wallet, but what’s different is that when you link Metamask to a website, there will be a prompt to allow the website to access your details on Metamask, similar like how we link our debit or credit card to a website that will ask for confirmation via the 6-pins provided from an SMS either from Visa or Mastercard company.
By clicking on the “Allow” or “Sign” button once the pop-up request is shown in the above screenshot, essentially the owner allows the origin (in the above screenshot, the origin is the polygon network) to have access to the Metamask wallet. This access can range from just-read access to allowing all sorts of transactions including the transfer of crypto assets to another account. (change to visual)
The victims of crypto phishing scams usually fall for these easily and thus lose their crypto assets just with a click.
Like how we constantly see new technology emerge, these scammers tend to find new & better ways to target their victims. The latest phishing scam is the iCloud phishing scam.
iCloud Phishing Scam
Metamask team issued a warning to all Apple users on the 18th Apr 2022 to disable iCloud backup for Metamask apps. This warning came after an NFT collector with Twitter handle @revive_dom lost his collection of NFTs


In this case, the scammer was able to access the seed phrase of Metamask, which means scammer has the full access to all the crypto assets within the Metamask. Once the owner provides the iCloud access to the scammer, the scammer was able to use the seed phrase and login into the Metamask as the “owner” with full access & able to do transactions from that wallet.
Thus, the Metamask team has advised all Apple users to turn off the backup on iCloud for Metamask to prevent a similar scam from happening.
Other Real-life Case Scenarios
Taiwanese pop star, Jay Chou lost his Bored Ape Yacht Club NFT through a phishing scam, in which his NFT was valued initially at 133 ETH and in which it was sold for 155 ETH later.
Singaporean rapper, Yung Raja faced a similar situation when he was fallen onto the same type of scam after clicking on a fraudulent link on Twitter, losing US$70,500 (~20 ETH).
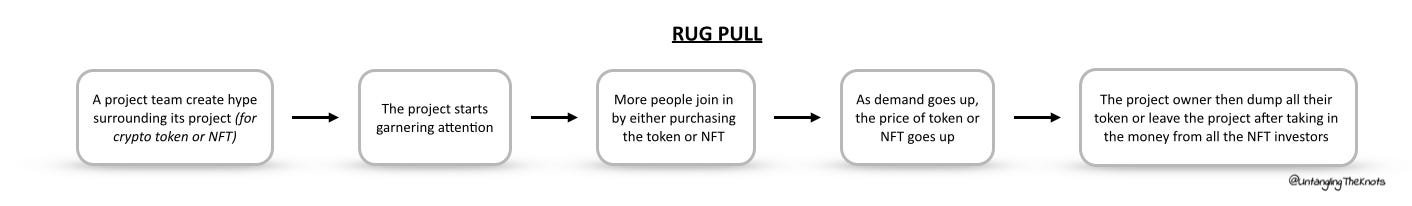
3. Rug Pull
Rug pull scam is literally what it means. Imagine standing on a rug and someone pulling the rug, you will be imbalanced and fall down.
In the crypto space, many are looking for the next big thing aka alpha (project or token expected to go big hence providing lucrative return). That prompted scammers to leverage this scam method as a way to garner fast money from people.
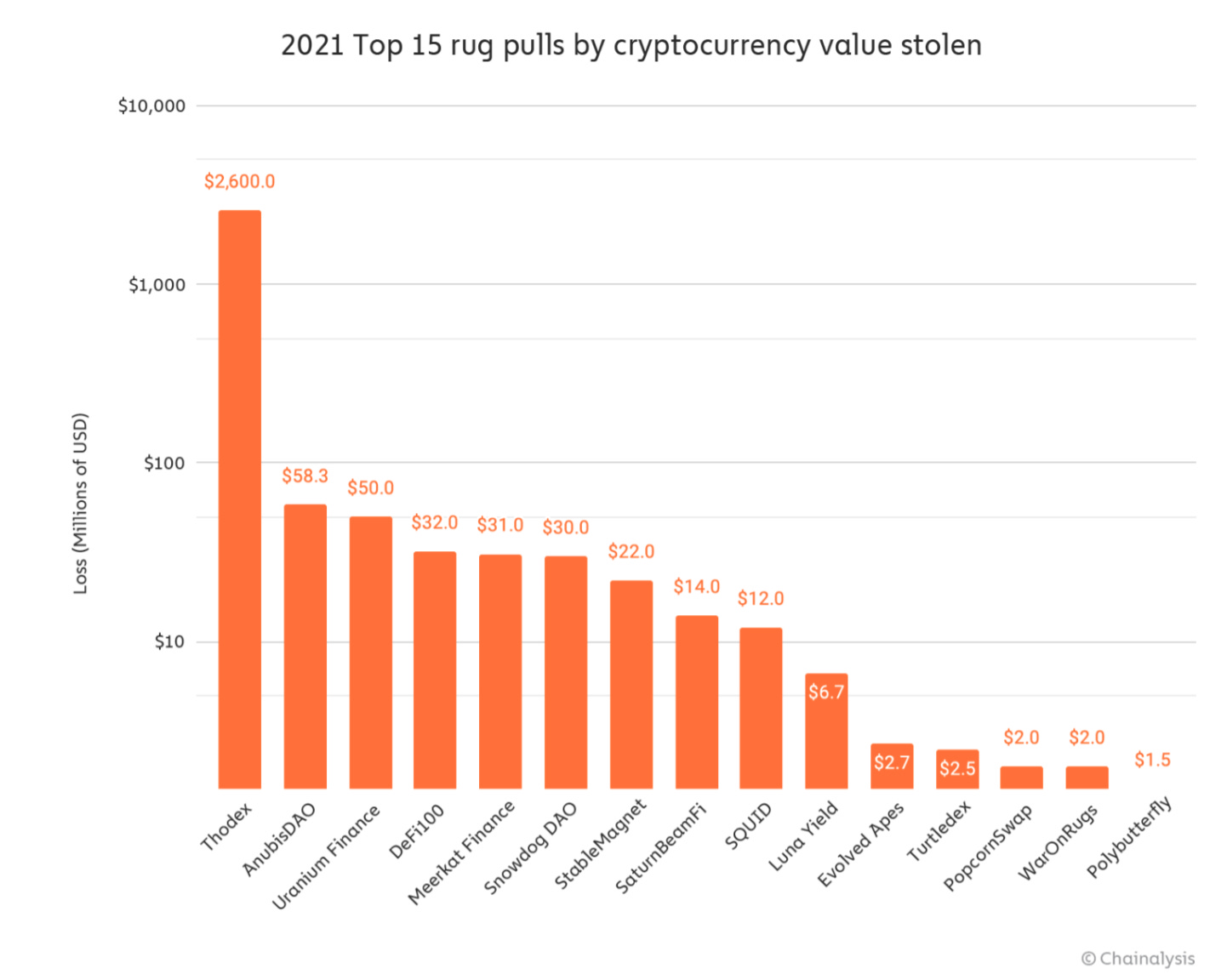
Rug pulls have become a major form of crypto fraud, especially in the year 2021 onward, making up nearly one-third of crypto scams and costing users about $2.8 billion last year according to Chainalysis, a blockchain data platform.
Promising lucrative returns & high-potential projects are ways how the below most Token or NFT projects garner attention & get people to buy in.
The rug pulls usually happen when the hype is almost at its peak, with Token showing high valuation or when people actually cash in for NFT. The team then disappear with the money, leaving the victims mourning over the lost money.
Below are some of the examples of Token or NFT projects involved in the rug pull scam. The project owners created hype for their projects and subsequently left with all the profits once the valuation is high enough (for the token) or once NFTs are minted (for NFT projects).
Rug pull scam in the crypto space is not just limiting to token or NFT projects. Some of the largest rug pull scams last year were Defi (Defi, short for decentralized finance which means it is a finance platform that is decentralized without any authority unlike a bank) projects and crypto exchange.
Top 2 Rug Pulls in 2021
4. Pump & Dump
Pump & dump is a market manipulation strategy that is used to promote and convince other investors to buy the token and wait to sell it off once it reaches inflated pricing.
This strategy has been long executed in the traditional stock trading market. While this is similar to the rug pull strategy, the difference here is that rug pull is executed by the founding team by throwing the project or token away while pump & dump can be executed by anyone.
Dogecoin, a meme coin that has been favored by Elon Musk where we can see him tweeting about it frequently, has shown a spike in the pricing in the past year.

Another pump & dump method is initiated by high buying power individuals (aka “whale” in crypto lingo), in which their purchase would help to push the token pricing up, and once the token shows a higher spike, they would dump it to profit.
5. Initial Coin Offering (ICO) Scam
Unlike Initial Public Offering (IPO), where well-established private companies go public once they get a certain valuation, ICO works differently. ICO is the equivalent of an IPO for a crypto company. But what makes ICO different from IPO is that anyone can raise ICO.
With less regulation within the ICO scope, the funds that are lost due to fraud or incompetence may never be recovered. It is no wonder that this has become another method that scammers use to their advantage.
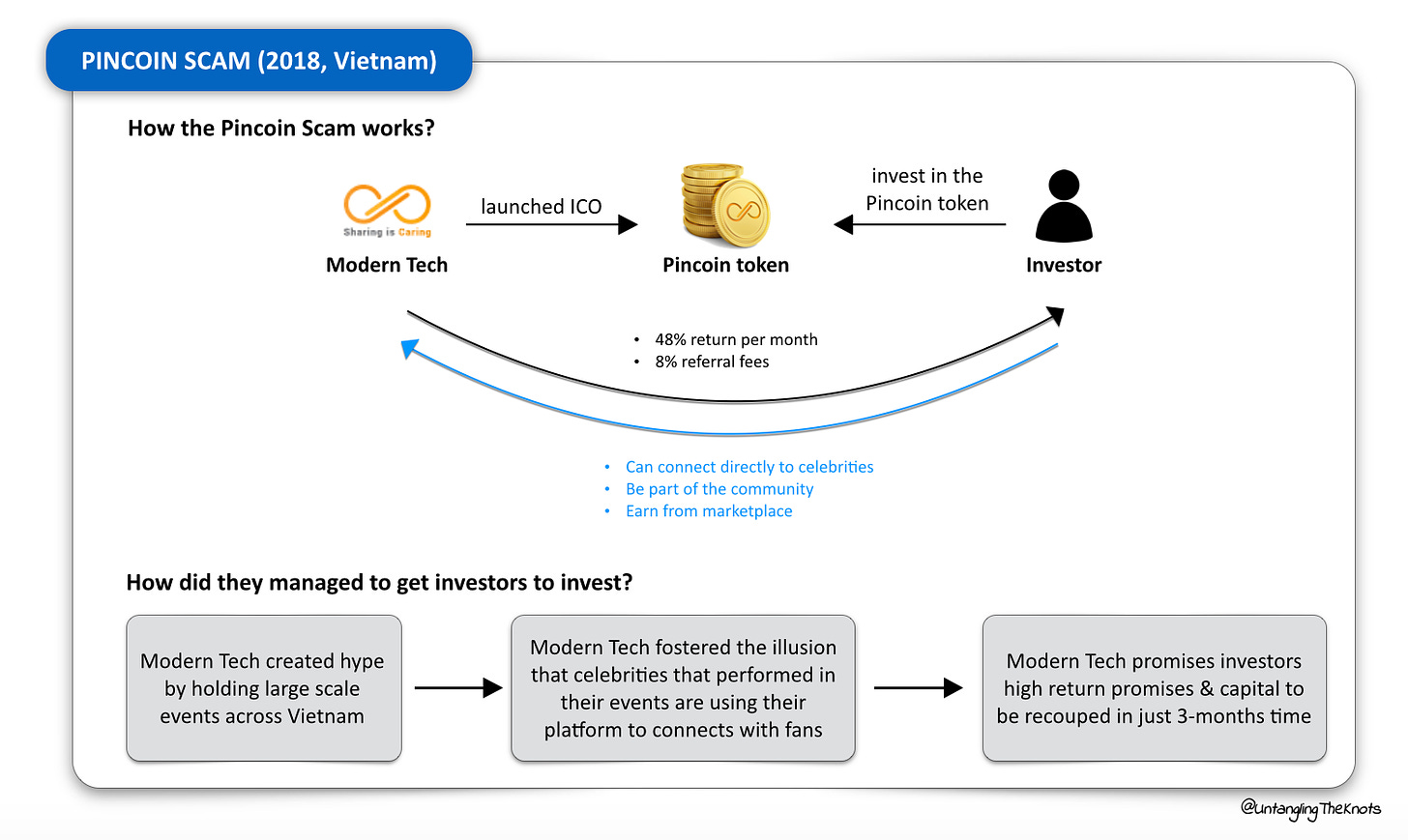
As early as back in 2017 to 2018, Asian countries have seen ICO scams at large. One of them is the Pincoin scam, which happened in Vietnam.
How to Avoid Falling Victim to Scams
1. Do your own due diligence aka do your own research (DYOR)
Read the project’s white paper
Usually, most projects would attach a white paper (proposal) to their website & by reading the white paper, you will be able to understand the business models and the long-term plan of the project.
Make sure the projects are verified
Some notable verification firms like Certik which does audits of Web3 firms help to ensure that the project is legitimate.
2. Invest in tools as a way to mitigate the risk of getting scam
Invest in a cold wallet
Similar to the concept of pendrive, a cold wallet is disconnected from the Internet unlike Metamask, which is a hot wallet. Cold wallets (or known as hardware wallets) prevent easy access by scammers especially if you have a high valuation of crypto assets. Examples of cold wallets are Trezor & Ledger.
Invest in insurance for your NFT or crypto
Services provided by Coincover helps to protect owners’ wallet and any crypto assets including NFTs in the wallet from malicious activity while offering an insurance-backed guarantee should anything happen.
3. Safety precaution by doing the necessity
Double & triple check any link or request approval prompt from anyone
If in doubt, do not press approved or reach out to the respective team to get further clarification.
Turn off iCloud backup / Do not put any information related to your crypto wallet into shared drive
Like how the iCloud phishing scam has shown, once a scammer hacked into your drive, it is easy to get access to your crypto wallet with the 12-words seed phase.
4. Stay connected & updated
Join the community in the Discord/Telegram group
Get updates and clarity from the team directly in the community group. The best way to get more information is from the peers who believe in the project, but do know when to filter certain information.
The In-Between
The gray area in crypto falls within the ideal way to move forward. While decentralization seems to be a perfect way, in reality, are we ready to embrace both the good and the downside of it?
Perhaps the beauty lies in the synergy of decentralization and centralization as we embark on this journey with an increased focus on security, law enforcement, and eventually adoption by the mass.
TLDR
By putting both spectrums in the big picture, we could see how things are not just from one perspective. Instead of allowing media to you via the hype created which eventually ignites the FOMO-ness to be part of the next big thing, it’s important to constantly put more research & understanding your risk appetite better - what you can afford to lose.
Extensive due diligence & study of past case studies are essential to ensure that we do not fall victim to any of these potential similar scams. As we see technological advancement evolve, similarly scammer does improve their ways to scam people. This is why it is essential to not invest more than you can afford or keep it at a lower ratio to your total net worth.
If anything sounds too good to be true, perhaps it is.
Disclaimer: I am not affiliated with or sponsored by any of the projects mentioned in this article at the time of writing.